Album Collection has a shell company in Hawaii? (14)
2023.10.02 16:24 Mariko Tsuji
Working with white-hat hackers to find the real app operators.

(Illustration by qnel)
Nonconsensual, sexually explicit images were traded through the smartphone apps Album Collection and Video Share. Child sexual abuse images were also being traded. I have been investigating this issue since last summer and have reported on it in this series.
These apps have been downloaded over hundreds of thousands of times. App users further spread the photos and videos they obtain therein online. The full extent of the damage is immeasurable.
The apps have gained many users because Google and Apple, which dominate Japan’s smartphone app market, listed them in their respective app stores: Apple listed both apps and Google listed Video Share. Six months after starting this series, in April 2023, Google removed Video Share from its store.
However, I still had not uncovered the identity of those who created and operate both apps — and who are profiting from the in-app trade in illegal sexual images.
I have now identified the operator of Album Collection. I will share the details over a series of articles, publishing every Thursday.
User arrested, after earning 15 million yen
Album Collection first appeared on Apple’s App Store in 2017. The description on the site says that Album Collection allows users to easily send and receive large amounts of photos and videos. It’s not obvious at first that sexually explicit images are being exchanged.
For example, Album Collection uses the following promotional phrases on its App Store page.
Share photos and videos of your graduation trip or school trip with everyone by simply sending your password!
Easily share your precious family photos and memories!
Easily share photos and videos of your girlfriend or boyfriend!
However, in reality the app is a hotbed of crime.
Passwords for obtaining child sexual abuse images and hidden camera footage are still being exchanged on social media. On one online message board, about 1,200 passwords were posted in one hour, with a total of more than 67,000 passwords shared on the site.
Most of the posts indicated that the content would include children. When put into the app, most of the passwords unlocked child sexual abuse images.
One user has even been arrested. He sold obscene images and also established an online message board where users could post Album Collection passwords for sexually explicit images. He was arrested in October 2022 on multiple charges. He had earned approximately 15 million yen (roughly $101,500) from posts and advertising revenue.
Pillar of business: selling sexually explicit images
Album Collection’s terms of service prohibit the trading of sexually explicit images, including, of course, images that violate the law.
In addition, Album Collection’s website has included the following statement on its home page since at least in 2020.
Recently, there has been an increase in the number of submissions that violate laws, regulations, and the terms of use.
Some malicious users have ignored warnings from the Album Collection Executive Committee, and even after deleting offending photos, re-submitted them under a different ID.
We are currently in the process of upgrading the system to strengthen measures against malicious violators.
We ask all users to refrain from committing any illegal acts or violations of the terms of use in Album Collection.
Album Collection Executive Committee
However, this reminder and the terms of use are contradictory.
The App Store has an age restriction on the use of Album Collection. The app information section states that it contains “sexual expressions or nudity” and “adult or obscene themes.”
When creators list their app on the App Store, they are required to report the frequency of violent and sexual images in their apps. This information is used to set age restrictions.
In other words, they are self-reporting the presence of obscene images, even though their terms of use prohibit trading obscene images.
I believe that sexually explicit images are the central pillar of Album Collection’s business. In fact, in over a year of reporting on Album Collections, I have never seen school trip or any other kind of feel-good photos exchanged. All are sexually explicit images, including some that are illegal.
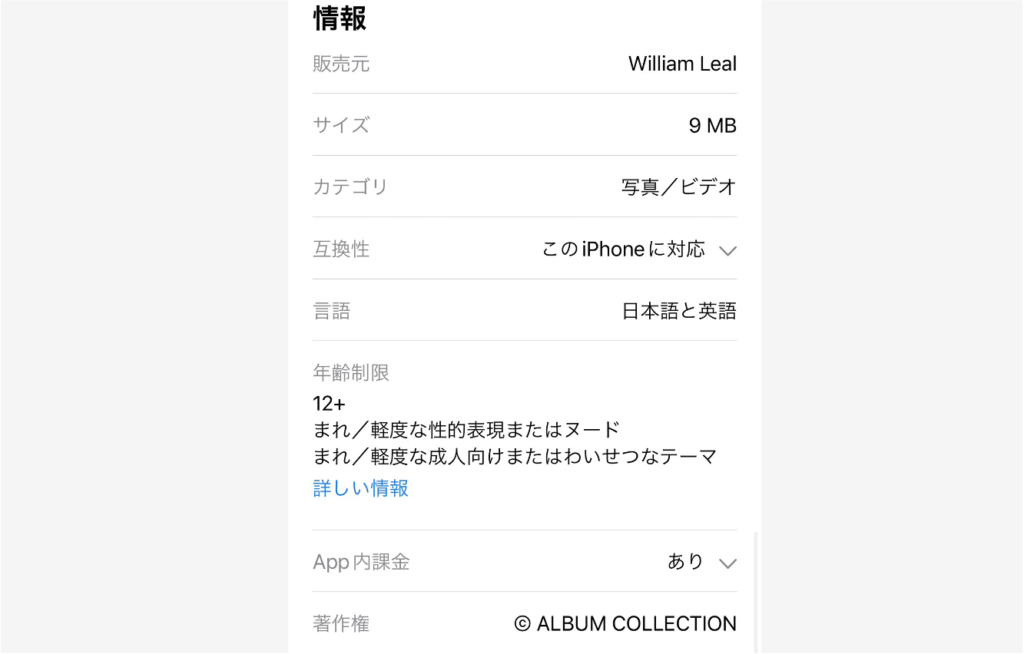
Album Collection is marked as age restricted in the app store.
The three official names
I had a feeling that something else was not quite right as well — the name of the operator.
The earlier reminder was attributed to the “Album Collection Executive Committee.” The contact information listed in the terms of use was also this committee. However, why would the creators and operators of an app call themselves a “committee”?
In the App Store, a non-Japanese name was listed as the distributor.
William Leal
Had the app been created by this individual?
Apparently not. A closer look at Album Collection’s website revealed that “Album Collection is a site operated by Eclipse Incorporated.”
So far, three names had been given for the creators and operators of Album Collection.
Album Collection Executive Committee
Eclipse Incorporated
William Leal
I decided to look into “Eclipse Incorporated,” which I could surmise was a company.
A company established in Hawaii, where anyone can do so
Eclipse Incorporated was a company registered in Hawaii. I found the following information on the Hawaiian state government website:
Registered: Nov. 6, 2018
Business purpose: Internet-related service
Executive: LEAL, WILLIAM
However, although Eclipse claimed to be an internet-related service company, it did not have a corporate website. How was it able to do business?
I wondered whether this was just a shell company.
It’s not difficult to establish a company in Hawaii. You do not have to be a U.S. citizen or a resident of Hawaii to do so, as long as you have a local address to register. The cost of registering a company in Japan is about 250,000 yen (roughly $1,700), but in Hawaii it is only $50.
The registration process can be completed in one or two weeks by outsourcing to an agent or lawyer. These agents will also prepare the address for registration. There is no need to visit Hawaii.
If “Eclipse Incorporated” was a shell company with no real activity and “William Leal” was a fictitious person, it wasn’t possible to grasp the reality of Album Collection just by searching based on the information the operators had made public. Was there another way to search?
While pondering this question, I remembered the existence of information security professionals known as white-hat hackers.
After doing some research, I found some individuals who had previous experience investigating illegal sites and tracking down their operators. I decided to contact them immediately.
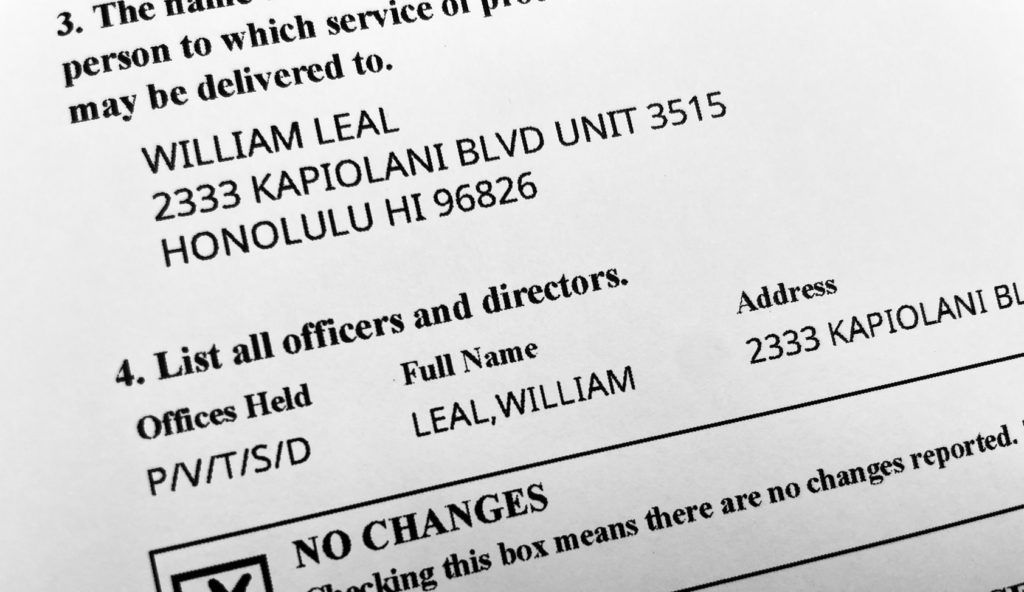
An annual report from Eclipse Incorporated, a company registered in the state of Hawaii
OSINT also used to expose war crimes
In May 2023, two white-hat hackers visited Tansa’s office.
The pair — who go by the names Cheena and Retr0 to keep their personal information confidential — are both Japanese youths in their 20s. When I gave them an overview of the investigation by email, they immediately responded that they would help.
White hats are professionals who have acquired in-depth knowledge of IT. Their main job is to manage a company’s information security and deal with cyber attacks.
Recently, a method called Open Source Intelligence (OSINT), which involves collecting various publicly available information and cross-checking and analyzing it to find new facts, has been attracting attention.
This approach is also being applied to journalism. Bellingcat, an investigative journalism organization based in the Netherlands, has used it to uncover information about the Syrian government’s war crimes and identify false information from Russia about its invasion of Ukraine.
Using OSINT, it might be possible to find information about the operator of Album Collection that had been previously out of reach.
Focusing on the payment system and emails
Upon entering Tansa’s office, Cheena and Retr0 quickly introduced themselves and got straight down to business. They took out their computers and examined Album Collection and Video Share’s sites in turn, sometimes using terms that I didn’t understand. But they had a serious look in their eyes.
The pair looked at the issue from their professional point of view and delved into points that I normally wouldn’t notice.
One example was the website’s payment system. If a company is selling illegal products, it may refuse to use common payment systems. For this reason, a less-regulated company’s system is often used on websites where child sexual abuse images and other illegal products are sold.
They also looked into the server that Album Collection used for sending emails, using an email exchange I had previous had with the unknown app operators.
Having struggled so far with only the operator’s public information, I was confident that this would move my investigation forward. If we identify the operator, we can hold them directly accountable.
Using their self-taught skills to help people
Both Cheena and Retr0 taught themselves programming and OSINT skills.
“I’ve been interested in programming since I was in middle school, and I learned by watching and copying others and following my interests,” Retr0 said.
He cooperated with my investigation because he thought the perpetrators’ behavior was unethical.
“If you think for a moment about how serious the damage is to the people whose photos are being sold, you would understand [that it’s wrong to sell them]. So why are they doing this?” Retr0 said. “I want to use my skills to treat others with kindness.”
In 2017, Cheena identified the operator of the website Manga Village, which offered pirated copies of illegal manga and magazines, and provided information to the police.
“I began cooperating with reporting out of intellectual curiosity to see if my skills could help break through injustices and problems on the internet.”
In the past, he have cooperated with Japanese public broadcaster NHK to investigate the operators of websites where the sale of child sexual abuse images is rampant.
“In order to evade being tracked, illegal websites also often disguise their public names and create offshore companies with no real activities to help with such.”
Cheena, Retr0, and I worked closely together to further the investigation. We used a secure messaging tool to share what we found. I usually received messages from them late at night or at dawn.
We came to see that there was another application tied to Album Collection.
And, from there, all at once, we arrived at a person.
To be continued.
(Originally published in Japanese on Sept. 14, 2023.)
Uploaded and Re-Uploaded: All articles
 Newsletter signup
Newsletter signup